Overview
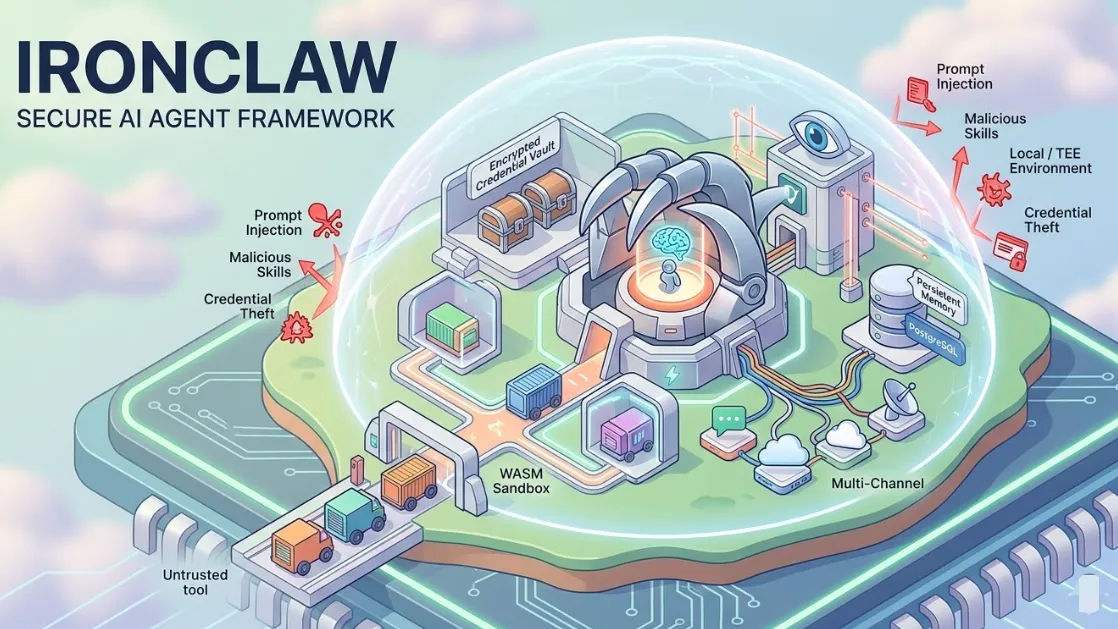
IronClaw is an open-source AI assistant runtime and personal agent framework written in Rust. It is a complete reimplementation of OpenClaw with a laser focus on privacy, transparency, and security. Every untrusted tool runs in an isolated WASM sandbox, credentials are stored in an encrypted vault and never exposed to the LLM, and the entire system can run locally or inside hardware-backed Trusted Execution Environments (TEEs) on NEAR AI Cloud.
Built on the philosophy that "your AI assistant should work for you, not against you," IronClaw eliminates the common risks of prompt injection, malicious skills, and credential theft that plague other agent frameworks.
Key Features
- Security-First Architecture: WASM sandbox with capability-based permissions, network allowlisting, outbound leak detection, and rate limiting.
- Encrypted Credential Vault: Secrets are injected at the network boundary only for approved endpoints; the LLM never sees raw keys or passwords.
- Trusted Execution Environments: Optional one-click deployment in hardware-isolated TEEs on NEAR AI Cloud.
- Self-Expanding Tools: Dynamically build and register new WASM tools via natural language; full MCP protocol support.
- Persistent Memory & Workspaces: Hybrid full-text + vector search over PostgreSQL with pgvector, plus secure workspace filesystem.
- Multi-Channel & Always-On: REPL, HTTP API, Telegram, Slack, webhooks, cron routines, parallel job execution, and automatic self-repair.
- LLM Flexibility: Works with NEAR AI, Ollama, OpenRouter, Together AI, AWS Bedrock, and any OpenAI-compatible endpoint.
Security Highlights
IronClaw implements defense in depth:
- Prompt injection detection and sanitization policies (Block/Warn/Review/Sanitize).
- Supply-chain verification with cargo-deny.
- Fuzz testing on all untrusted input parsers.
- No telemetry by default; full audit logs.
- Memory safety guaranteed by Rust.
Deployment Options
- Local: Install via Homebrew, MSI, or build from source (Rust 1.85+ required). Runs entirely on your machine with PostgreSQL.
- Cloud: One-click deployment on NEAR AI Cloud inside TEEs. Starter tier free (pay-per-use), Pro+ available for multiple agents.
Getting Started
- Install via
brew install ironclaw(macOS/Linux) or download the MSI (Windows). - Run
ironclaw onboardto set up PostgreSQL, NEAR AI account, and encrypt secrets. - Start the REPL with
ironclawor connect via Telegram/Slack using the provided setup guides.
Full documentation, including LLM provider setup and channel integrations, is in the /docs folder of the repository.
Use Cases
- Personal life automation (email, calendars, research, shopping).
- Professional knowledge work (CRM workflows, outreach, coding agents).
- Secure enterprise agents that must handle real credentials without risk.
- Local-first AI that respects user privacy and never phones home.
Architecture
IronClaw consists of an agent loop, router, scheduler, workers, orchestrator, web gateway, routines engine, tool registry, and a dedicated safety layer — all compiled in Rust for performance and safety.
License & Contributing
Dual-licensed under Apache 2.0 and MIT. Contributions welcome; every PR includes a security risk assessment.
Latest release: v0.18.0 (March 2026). Pre-built binaries and installers available on the releases page.